The Logic Verification Protocol.
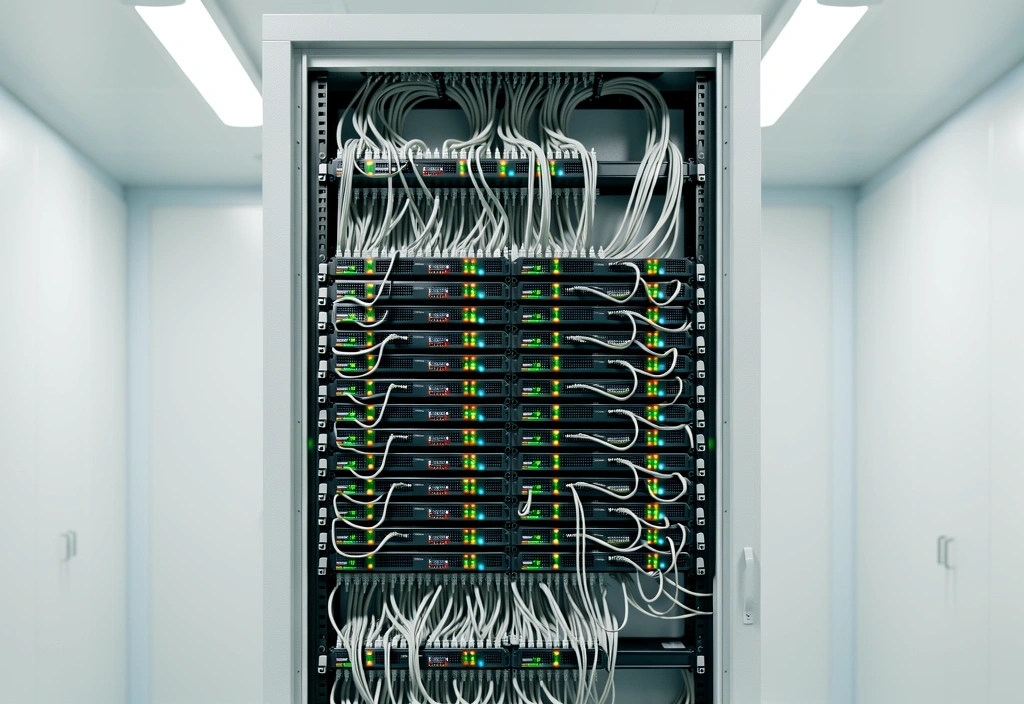
High-performance data systems require more than simple uptime. We implement a rigorous 5-step logic verification framework to ensure every architectural decision is mathematically sound and operationally resilient.

01. Structural
Logic Mapping
Before a single byte of data flows through a new architecture, our engineers perform a full logic mapping exercise. This involves identifying potential bottlenecks in the data path and verifying that the fundamental logic of the system aligns with enterprise-scale throughput requirements.
We treat data structures as physical assets. By visualizing the dependencies between disparate data silos, we eliminate the risk of circular references or recursive failures that often plague unverified global systems. This stage ensures the foundation is capable of supporting multi-terabyte daily ingest without degradation.
Current Verification Focus
- Redundancy pathing for distributed cloud environments.
- Logic-branching optimization for real-time analytics.
Controlled Environment Stress Testing
We simulate high-velocity data failure scenarios within our Osaka-based Logic Lab. This allows us to observe how systems behave under extreme pressure before they are deployed into live production.
Transactional Atomicity
Verifying that all data transactions are completed fully or not at all. Our verification prevents partial data writes that lead to systemic corruption in financial and enterprise databases.
Latency Consistency
We measure the logic overhead of every architecture. Our goal is a sub-millisecond deviation in response times, regardless of the geographic location of the data source.
Encryption Handshakes
Security logic is audited to ensure that data in transit and at rest remains inaccessible to unauthorized entities while maintaining high-speed access for verified logic tokens.

Automated Constraint Analysis
We utilize proprietary tools to scan system logic for common failure patterns. This automated approach identifies logical contradictions that manual reviews might overlook, providing a first line of defense against system instability.
This phase is essential for modern data systems that integrate legacy components with new cloud-native logic. We ensure compatibility across generations of data architecture.
Live-Shadow Validation
Before switching to a new system, we run a "shadow" instance alongside your current operations. By comparing the logic outputs of both systems in person, we confirm that the new architecture performs as expected without interrupting existing workflows.
- Zero Downtime Transitions
- Real-time Comparative Logs
- Data Parity Enforcement
- Fault-Tolerance Mapping
Transparent Verification Data
At the conclusion of our verification process, every client receives a comprehensive Logic Integrity Report. We believe that trust is built through clear, verifiable data that proves your system is ready for the demands of the global market.
Schema Validation
A formal proof that your data schemas are optimized for querying and long-term storage scalability.
Logic Flow Analysis
Visualization of all logical decision points within your software and how they interact with core services.
Performance Benchmarks
Hard data on query speed, write latency, and system response times under concurrent user load.
Resilience Score
A measurement of the system's ability to recover automatically from network or hardware failures.
Ready to bridge the logic gap?
Secure your system's integrity with Osaka Global Logic. Our team is available to begin preliminary architectural audits this week.
Osaka Global Logic
Mon-Fri: 09:00-18:00 JST